A destruction certificate is the formal document that confirms your IT assets have been properly sanitised or physically destroyed. It is the final piece of the disposal puzzle, the proof that your data is gone and your equipment has been handled responsibly. But not all destruction certificates are created equal. Knowing what a good certificate should contain helps you evaluate whether your ITAD provider is giving you genuine assurance or just a piece of paper.
The Purpose of a Destruction Certificate
A destruction certificate serves as legal evidence that your organisation took appropriate steps to destroy data on disposed equipment. If you ever face a data breach investigation, an audit, or a compliance review, this certificate is what you point to. It demonstrates due diligence and shows that you engaged a capable provider who followed recognised standards.
For organisations subject to the Australian Privacy Principles, maintaining destruction certificates is part of meeting your obligations to take reasonable steps to destroy personal information when it is no longer needed. Under various industry regulations, from financial services to healthcare, these certificates may be explicitly required as part of your records retention.
Essential Elements
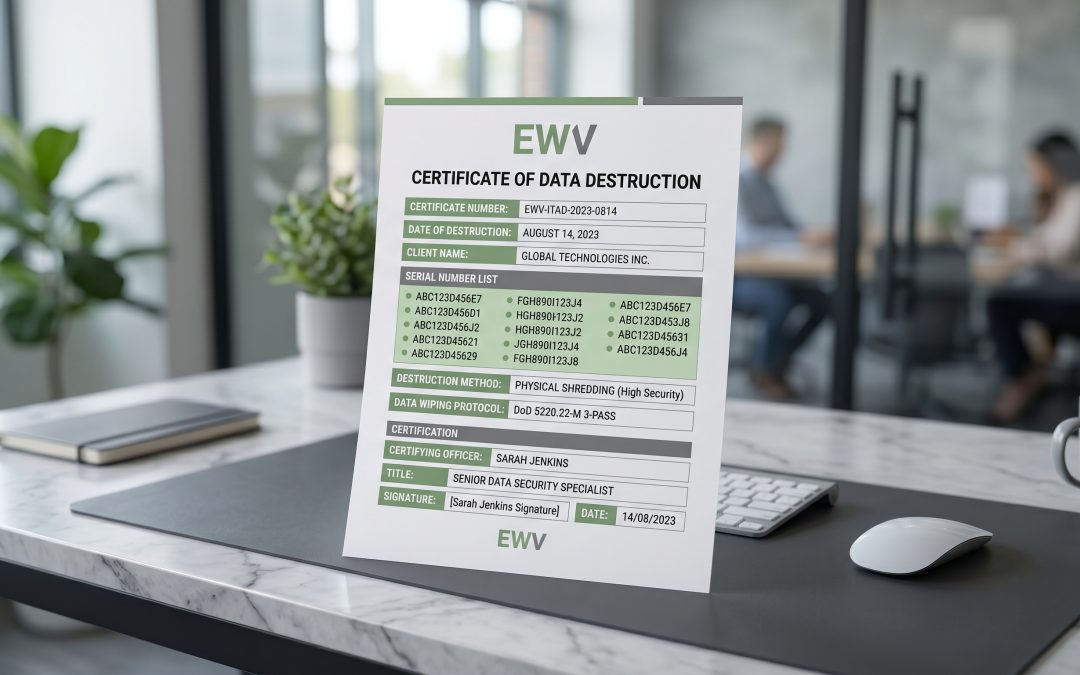
A comprehensive destruction certificate should include several categories of information. First, identify the provider: the full legal name of the ITAD company, their business address, relevant certifications (such as AS/NZS 5377, ISO 27001, R2), and the name and signature of the authorised person issuing the certificate.
Second, identify your organisation: the client name, contact person, and the site or project reference the disposal relates to.
Third, and most importantly, identify the assets. Every data-bearing device should be listed individually with its asset tag number, serial number, make and model, and the type of storage media it contained. Certificates that simply say “50 laptops destroyed” without individual identification are insufficient because they do not let you verify that specific devices were actually processed.
Destruction Method Details
The certificate should clearly state what was done to each device. For software-based data sanitisation, this means the wiping standard used (such as NIST 800-88 Clear, Purge, or Destroy), the specific software tool and version, the number of passes or the overwrite method, and a pass/fail result for each device.
For physical destruction, the certificate should state the method used (shredding, crushing, degaussing, disintegration), the particle size for shredding (which matters for compliance with some standards), and confirmation that the media was rendered unrecoverable.
For devices that received a combination of methods, such as degaussing followed by shredding, both steps should be documented.
Dates and Timestamps
Timing matters in destruction documentation. The certificate should include the date equipment was received by the ITAD provider, the date data destruction was performed, and the date the certificate was issued. For organisations with strict data retention policies, the destruction date is the one that matters most, as it is the date you can confirm the data no longer existed.
Some providers issue certificates weeks or even months after processing. Ideally, certificates should be issued promptly after destruction, while the processing is still fresh and records are easily verified.
Chain of Custody Reference
A good destruction certificate connects to the broader chain of custody. It should reference the collection or job number, link back to the manifest or inventory list that was created when equipment was collected, and confirm that the number of devices processed matches the number collected. Any discrepancies between what was collected and what appears on the certificate need explanation and investigation.
Understanding the full IT asset lifecycle helps put the destruction certificate in context as the final documentation milestone in a comprehensive process.
Digital vs Paper Certificates
While paper certificates with wet signatures were once the standard, digital certificates offer several advantages. They are easier to store, search, and retrieve during audits. They can include embedded verification features such as digital signatures and timestamps that are harder to falsify. And they can be integrated with asset management systems for automated reconciliation.
Whatever format your provider uses, ensure certificates are stored securely and retained for the period required by your organisation’s records management policy and any applicable regulations. Many organisations retain destruction certificates for seven years or more.
Verification and Spot Checks
Receiving a certificate is not the end of the story. Periodically verify that your certificates are accurate by conducting spot checks. This might involve visiting your ITAD provider’s facility unannounced to observe processing, requesting video evidence of destruction for high-security assets, cross-referencing certificate serial numbers against your internal asset register, or engaging an independent auditor to review your ITAD provider’s processes.
Trust but verify. A provider who welcomes scrutiny of their certification process is typically one you can rely on. One who resists inspection or cannot produce supporting evidence for their certificates should raise concerns about the value of the documentation they provide.
Storing and Managing Certificates
Create a systematic approach to storing destruction certificates. Link each certificate to the corresponding assets in your asset management system so that you can quickly locate the destruction record for any specific device. This becomes invaluable during audits, when you may need to demonstrate the disposal history of specific equipment at short notice.