Good Intentions, Hidden Risks
Donating old IT equipment to schools, charities, community groups, or employees is a generous and environmentally responsible choice. It gives functional technology a second life and supports organisations or individuals who might not otherwise afford it. However, donating equipment without properly destroying the data stored on it turns a good deed into a potential data breach, exposing the donor organisation and the individuals whose data is on the device to serious risk.
The desire to do something positive with old equipment can create a blind spot around data security. The reasoning often goes: “It’s just going to a school” or “The charity will reformat it.” But neither of these assumptions provides any assurance that data has been properly removed. The recipient may not have the technical capability to perform data destruction, and even if they do, the donor cannot verify that it was done correctly.
What Data Remains on Donated Equipment
Equipment being donated has typically been in active use for three to five years. During that time, it has accumulated a comprehensive collection of business data. Documents, spreadsheets, presentations, email databases, browser histories, saved passwords, cached credentials, and application data all reside on the storage media.
Even a basic office workstation used for general administrative tasks will contain the user’s email history, any documents they worked on or opened, temporary files created by applications, cached web content, and system logs that may include network credentials and activity records.
Devices used in specific business functions carry even more sensitive data. A finance department computer may contain accounting records and banking details. An HR workstation may hold employee personal information. A sales team laptop may contain customer databases and pricing information.
Formatting a drive or reinstalling the operating system does not remove this data. Standard formatting creates a new file system structure on the drive but does not overwrite the underlying data. Anyone with basic data recovery tools, freely available online, can recover files from a formatted drive within minutes.
Legal Obligations When Donating Equipment
The Australian Privacy Act requires organisations to take reasonable steps to destroy personal information when it is no longer needed. Donating a device with personal information still on it clearly fails this standard. The fact that the device was donated to a reputable organisation does not change the donor’s obligation to ensure data destruction before the device leaves their control.
If personal information from donated equipment is subsequently accessed by an unauthorised party, the donating organisation bears responsibility for the breach. A school receiving donated laptops has no obligation to protect the donor’s data, and the students, staff, or volunteers who encounter the data are not bound by any confidentiality agreement with the donor.
Victoria’s e-waste landfill ban, which came into effect on 1 July 2019, encourages the reuse and recycling of electronic equipment. This is a positive environmental policy, but it must be balanced with data security obligations. Reuse is only safe when proper data destruction precedes the transfer of equipment to new users.
How to Properly Prepare Equipment for Donation
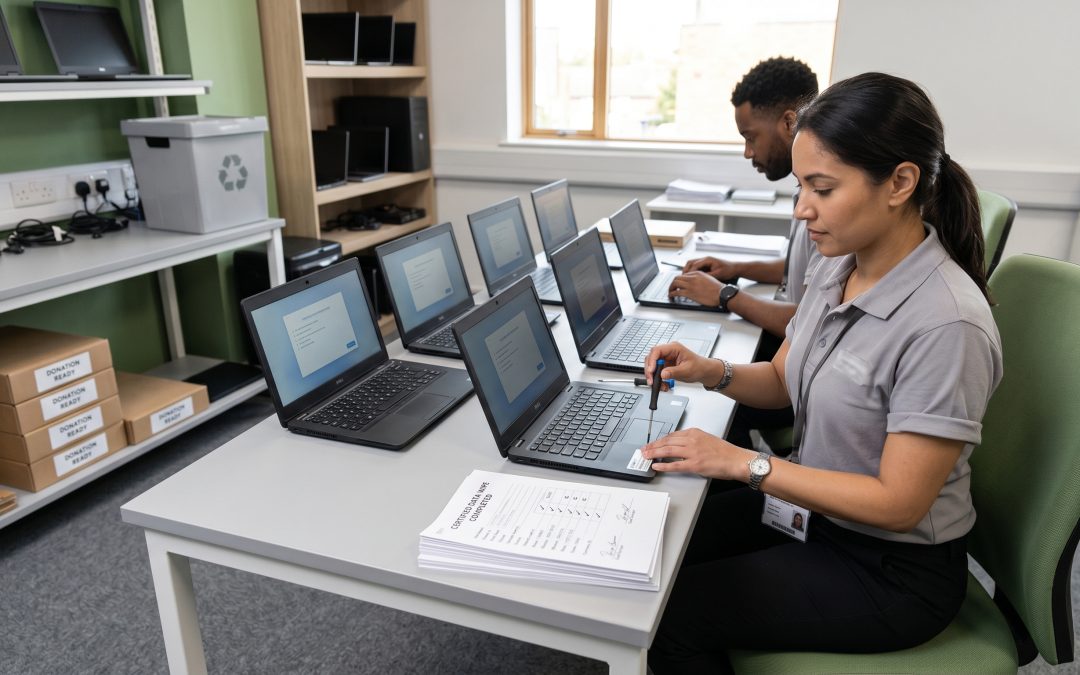
Before any device is donated, it must undergo verified data destruction. This is a non-negotiable step regardless of who the recipient is or how trustworthy they may be. The standard process involves backing up any data that needs to be retained, then performing a full disk sanitisation using tools that comply with NIST 800-88 standards.
After sanitisation, install a fresh operating system so the device is ready for the recipient to use. This is a courtesy to the recipient and also provides a functional verification that the device is in working order after the wipe process.
For organisations donating multiple devices, batch processing through a certified IT asset disposition provider is the most efficient approach. The ITAD provider can sanitise all devices to a verified standard, provide certificates of destruction for the donor’s records, and prepare the devices with fresh operating system installations ready for the recipient.
Certificates of destruction should be obtained and retained for every donated device. Even though the device is being given away rather than scrapped, the data on it has been destroyed, and the certificate documents this action for compliance purposes.
Donating to Specific Recipient Types
Schools and educational institutions are common recipients of donated equipment. These organisations have limited IT budgets and genuine need for functional computers. However, they also have students who are often technically curious and may explore the device’s storage more thoroughly than an average user. Ensuring thorough sanitisation before donating to schools protects against both intentional and accidental data discovery.
Charities and not-for-profit organisations may use donated equipment for direct service delivery, which could involve storing their own sensitive client data on the donated device. Starting with a clean, properly wiped device protects both the donor’s former data and the charity’s future data.
Employees who receive old equipment as a benefit of their employment are in a unique position. They are already familiar with the organisation’s data and may have used the very device being donated. Nonetheless, proper sanitisation should occur before handover. The employee may share the device with family members, sell it later, or dispose of it without considering the data it originally contained.
When Donation Is Not Appropriate
Not all equipment should be donated. Devices that stored highly sensitive data, such as servers that held customer databases, financial systems, or health records, may not be suitable for donation even after software-based sanitisation. For this category of equipment, physical destruction of the storage media followed by recycling of the remaining components is the more appropriate path.
Devices that are too old to be genuinely useful should be recycled rather than donated. Donating equipment that is slow, unreliable, or unable to run current software does not provide meaningful benefit to the recipient and may create frustration rather than value. Victoria’s e-waste recycling infrastructure makes it easy to recycle equipment that has reached the end of its useful life.
Making Donation Work Safely
Equipment donation is a worthwhile practice that supports both environmental sustainability and community organisations. The key is ensuring that data destruction is treated as a prerequisite, not an afterthought. By sanitising every device before it is donated and retaining certificates of destruction as proof, organisations can give generously while maintaining the data security standards that protect their business and the people whose information they hold.