Some IT equipment requires a higher level of care during disposal than standard office devices. Equipment that has processed classified information, sensitive financial data, health records, legal privileged material, or critical intellectual property demands elevated security measures throughout the entire disposal chain. Getting this right protects your organisation from data breaches, regulatory penalties, and reputational harm.
Identifying Confidential Equipment
The first step is knowing which devices in your estate warrant elevated handling. Confidential equipment typically includes servers that hosted databases containing personal information or financial records, executive laptops and devices used by senior leadership, devices used by legal, HR, finance, or compliance teams, equipment that processed health records or legal privileged information, development servers containing intellectual property or source code, and any equipment used in regulated environments (financial services, healthcare, government).
Your data classification framework should make this identification straightforward. If you do not have a formal classification system, now is the time to create one. Every device should have a known data sensitivity level before it enters the disposal process.
Elevated Security Requirements
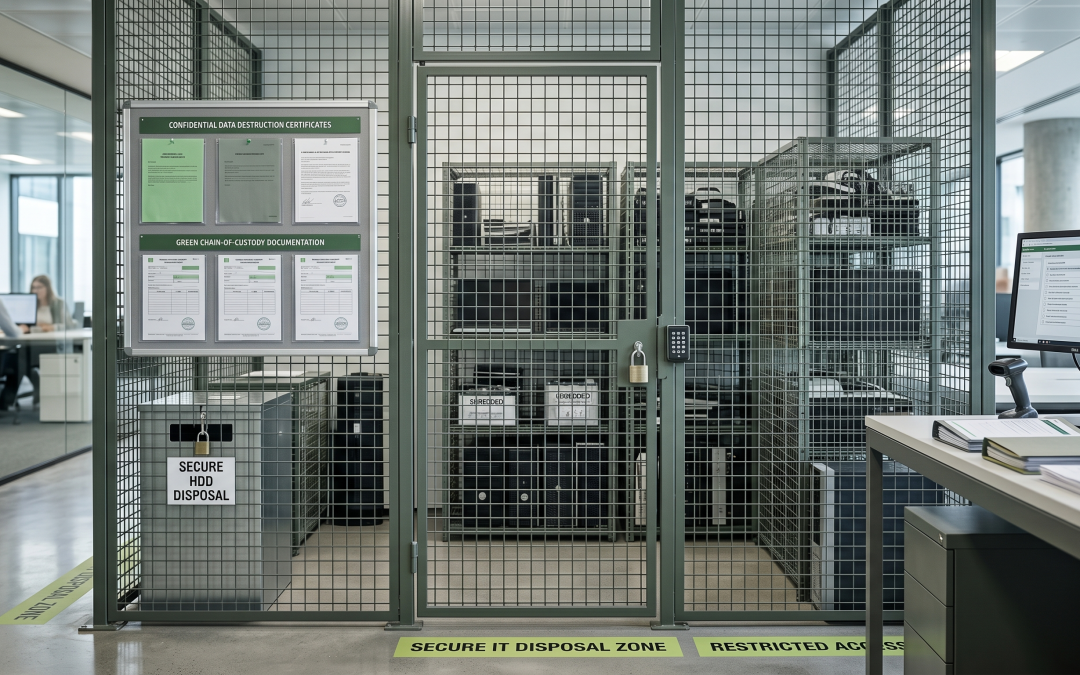
Confidential equipment needs stronger controls at every stage compared to standard disposal. During pre-disposal handling, devices should be stored in a locked, access-controlled area from the moment they are decommissioned. Access to this storage should be limited to named individuals, and entry should be logged. The time between decommissioning and data destruction should be minimised.
For data destruction, confidential equipment typically warrants either on-site destruction with witnessed procedures, or certified software sanitisation followed by physical destruction of the storage media. Software wiping alone, even when certified, may not meet the requirements for the most sensitive classifications. Following NIST 800-88 Purge or Destroy level sanitisation provides the appropriate assurance.
If equipment must be transported to an off-site facility for processing, use sealed, tamper-evident containers with GPS-tracked dedicated transport. The chain of custody documentation should track every handoff by name, time, and location.
Witnessed Destruction
For the most sensitive equipment, witnessed destruction provides the highest level of assurance. This means a representative from your organisation physically observes the data destruction process. For on-site destruction, your representative watches as drives are shredded, degaussed, or wiped. For off-site processing, your representative travels to the facility and observes the processing of your specific devices.
Video recording of the destruction process is an alternative when physical witnessing is not practical. The recording should clearly show each device’s serial number before destruction, the destruction process itself, and the resulting destroyed media. This recording becomes part of your compliance documentation.
Documentation and Certification
Documentation for confidential equipment disposal should be more detailed than standard disposal records. Beyond the normal destruction certificate, maintain a specific inventory of all confidential devices with serial numbers, names and signatures of everyone who handled the equipment, timestamps for every stage of the process, photographs or video of destroyed media, and the method and standard used for each device.
This documentation should be stored securely, with access restricted to authorised personnel. It may need to be retained for extended periods depending on your industry’s regulatory requirements.
Provider Requirements
Not every ITAD provider is equipped to handle confidential equipment appropriately. When selecting a provider for sensitive disposals, verify that they hold relevant certifications including ISO 27001 and AS/NZS 5377. Confirm that their staff have undergone appropriate background checks. Inspect their facility security measures personally. Review their procedures for handling high-security assets. Check their insurance coverage for data breach liability. And ask for references from clients with similar security requirements.
Your provider selection process for confidential disposals should be more rigorous than for standard equipment, with a heavier weighting on security capabilities relative to price.
Legal and Regulatory Considerations
Various regulations impose specific requirements for disposing of confidential data-bearing equipment. The Australian Privacy Principles require reasonable steps to destroy personal information. APRA CPS 234 sets information security expectations for financial institutions. Health records legislation governs the disposal of medical information. Government security classifications impose specific destruction requirements for classified material.
Understand which regulations apply to your specific equipment and data types, and ensure your disposal procedures meet or exceed the applicable requirements. When in doubt, consult with your legal and compliance teams before proceeding.
Internal Procedures
Build confidential equipment disposal into your ITAD policy as a distinct process with its own procedures. Staff who handle confidential equipment should be specifically trained on the elevated requirements. Regular audits should verify that the procedures are being followed consistently. And any deviations from the established process should be investigated and addressed promptly.