by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
IT equipment trade-in programs focus on value recovery, not data security. Learn what happens to your data when you trade in devices and how to protect your organisation before participating in trade-in programs.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Repurposing old IT equipment internally without wiping it gives new users access to previous users’ data. Learn why internal device transfers still require proper data sanitisation to maintain access controls.
by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
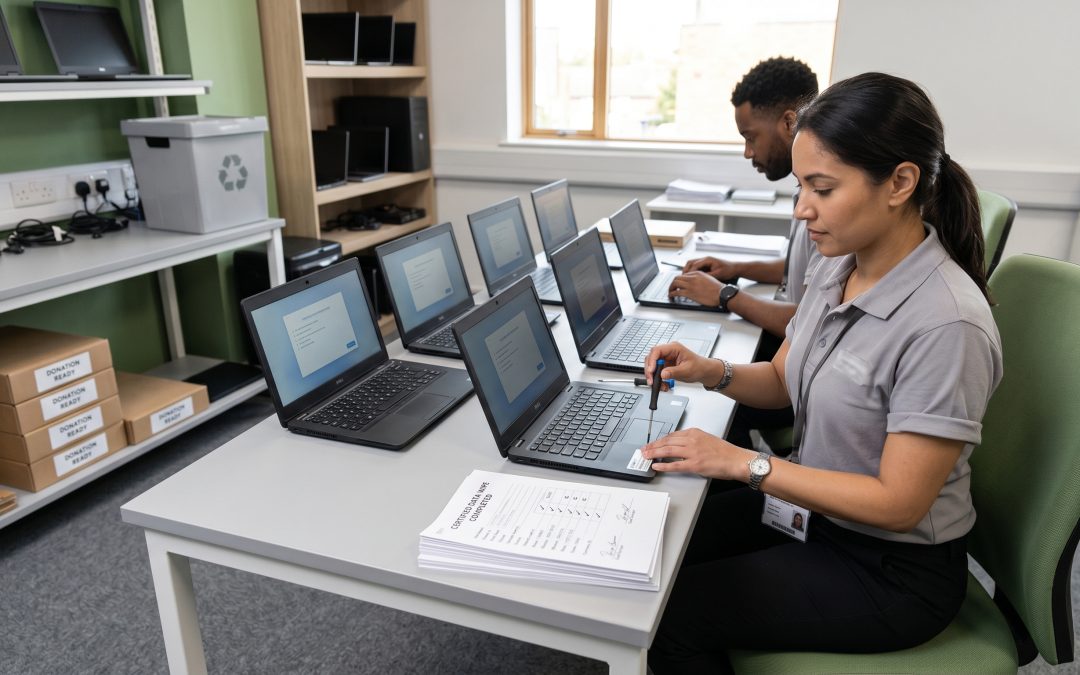
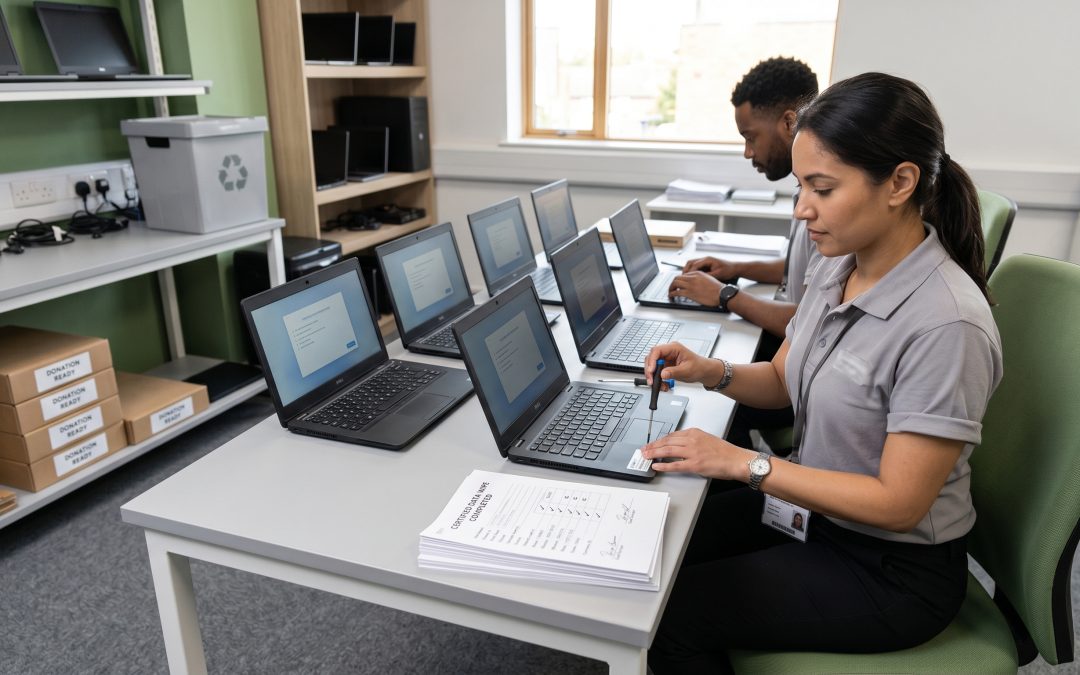
Donating old IT equipment without proper data destruction turns a good deed into a data breach risk. Learn how to wipe devices properly before donating computers to schools, charities, or employees.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Warranty returns expose your business data to repair centres, logistics providers, and refurbishment operations. Learn how to protect data before sending devices for warranty repair and explore keep-your-drive programs.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
A failed hard drive is not the same as a wiped hard drive. Data recovery specialists can extract information from drives that appear completely dead. Learn why failed drives still require secure data destruction.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Acquiring a business means inheriting its IT equipment and all the data stored on it. Learn how to assess inherited IT assets, identify data risks, and establish clean data governance after a business purchase.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Deceased estate electronics contain years of personal data that must be handled carefully by executors. Learn about legal obligations, device access, data preservation, and proper disposal of inherited electronic devices.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Insurance claims on damaged IT equipment can expose sensitive business data when devices are surrendered to insurers or salvage dealers. Learn how to protect data during the claims process and prevent breaches from damaged devices.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Contractor and temporary worker device returns require careful data security management. Learn how to establish processes for collecting, sanitising, and tracking IT equipment used by external workers.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
BYOD policies create unique data destruction challenges when employees leave. Learn how to use MDM selective wipe, containerisation, and offboarding procedures to protect company data on personal devices.