by E-Waste Victoria | Apr 13, 2026 | Education, IT Asset Disposition
Choosing the right ITAD vendor requires evaluating certifications, data destruction capabilities, environmental practices, security measures, reporting quality, and value recovery. Here is what to look for and what questions to ask.
by E-Waste Victoria | Apr 13, 2026 | Education, IT Asset Disposition
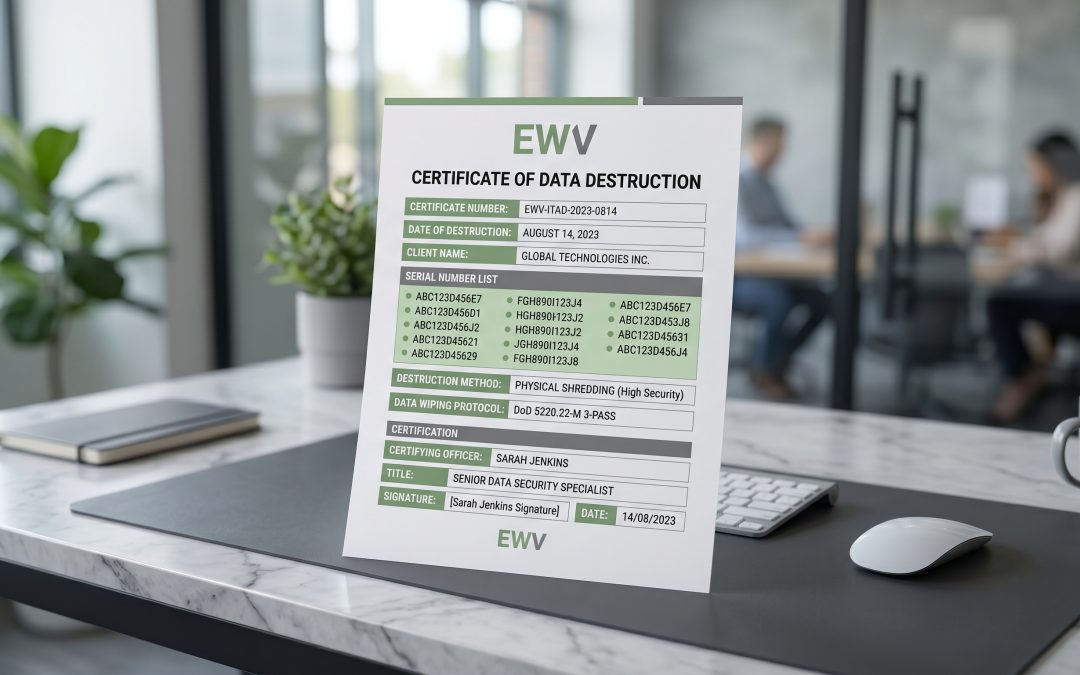
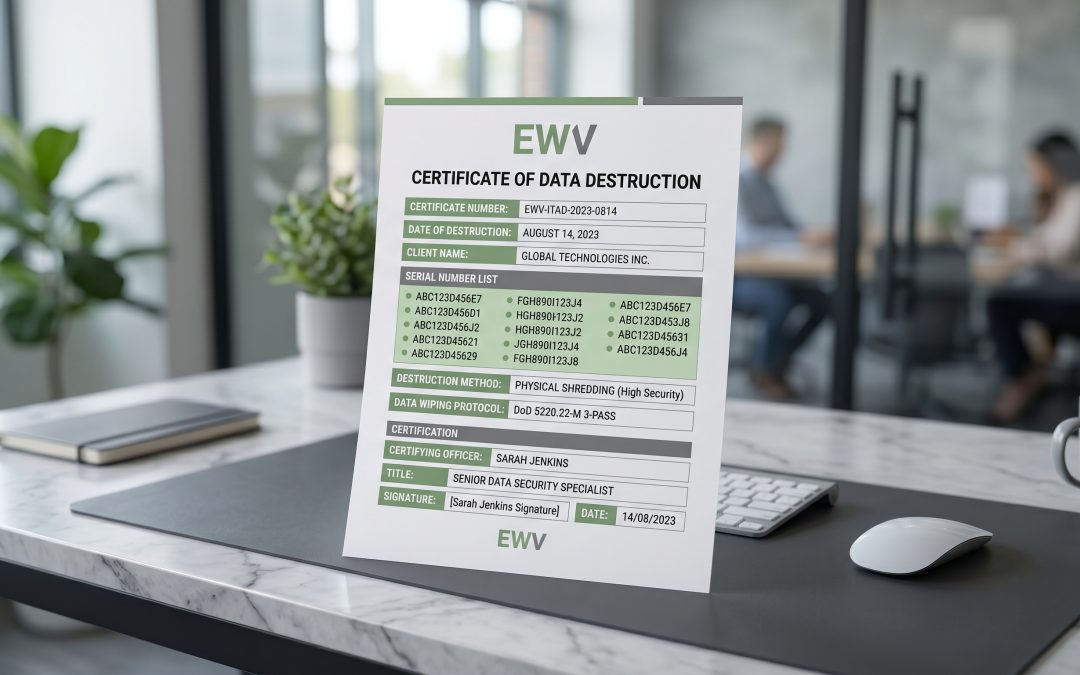
A destruction certificate proves your IT assets were properly sanitised or destroyed. Learn what essential elements to look for, including individual serial numbers, destruction methods, dates, and chain of custody references.

by E-Waste Victoria | Apr 13, 2026 | Education, IT Asset Disposition
A chain of custody tracks every IT asset from disposal identification through final destruction or resale. Learn why this documentation is essential for data security, regulatory compliance, and financial accountability.

by E-Waste Victoria | Apr 13, 2026 | Education, IT Asset Disposition
A thorough IT asset audit before disposal ensures no equipment is missed, identifies value recovery opportunities, and provides essential documentation for compliance. Learn the step-by-step process for auditing your IT estate.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Renewable energy monitoring systems store performance data, grid connection parameters, network credentials, and commercial information. As Australia’s first wave of solar and wind monitoring equipment ages, secure disposal is becoming an industry-wide priority.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Modern EV charging stations contain computers, payment terminals, communication modules, and extensive data storage. Secure decommissioning requires addressing payment data, user information, network credentials, and environmental disposal requirements.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Voice assistant devices store audio recordings, smart home configurations, network credentials, and detailed usage patterns both locally and in the cloud. Secure disposal requires addressing both on-device data and cloud-stored recordings.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Modern 3D printers store complete print job histories, proprietary design files, network credentials, and user data. Secure disposal requires identifying all storage points and treating these machines as data-bearing IT assets.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Modern robots store proprietary manufacturing processes, network credentials, facility maps, and production data across multiple internal components. Secure disposal requires identifying all storage points and using appropriate sanitisation methods.

by E-Waste Victoria | Apr 13, 2026 | Data Security & Destruction, Education
Digital twin platforms accumulate vast amounts of sensitive operational data across distributed infrastructure. Proper decommissioning requires identifying all data repositories, classifying sensitivity, and following established destruction standards.